Cyber Deception for Defense
AdversaryMeter
AdversaryMeter reconfigures your Cloud technologies to redirect attackers targeting your servers to tailored decoys. The result: trapped attackers, high-quality threat intelligence and precise KPIs.

Gather
Categorize the ongoing attacks (manual vs. automated), assess the technical capabilities of the attackers and evaluate their persistence over time despite IP rotations.
Deceive
Seamlessly integrate decoys within your authentic digital assets, which may include websites, access points, or critical infrastructure components.
Tailored Threat Intel
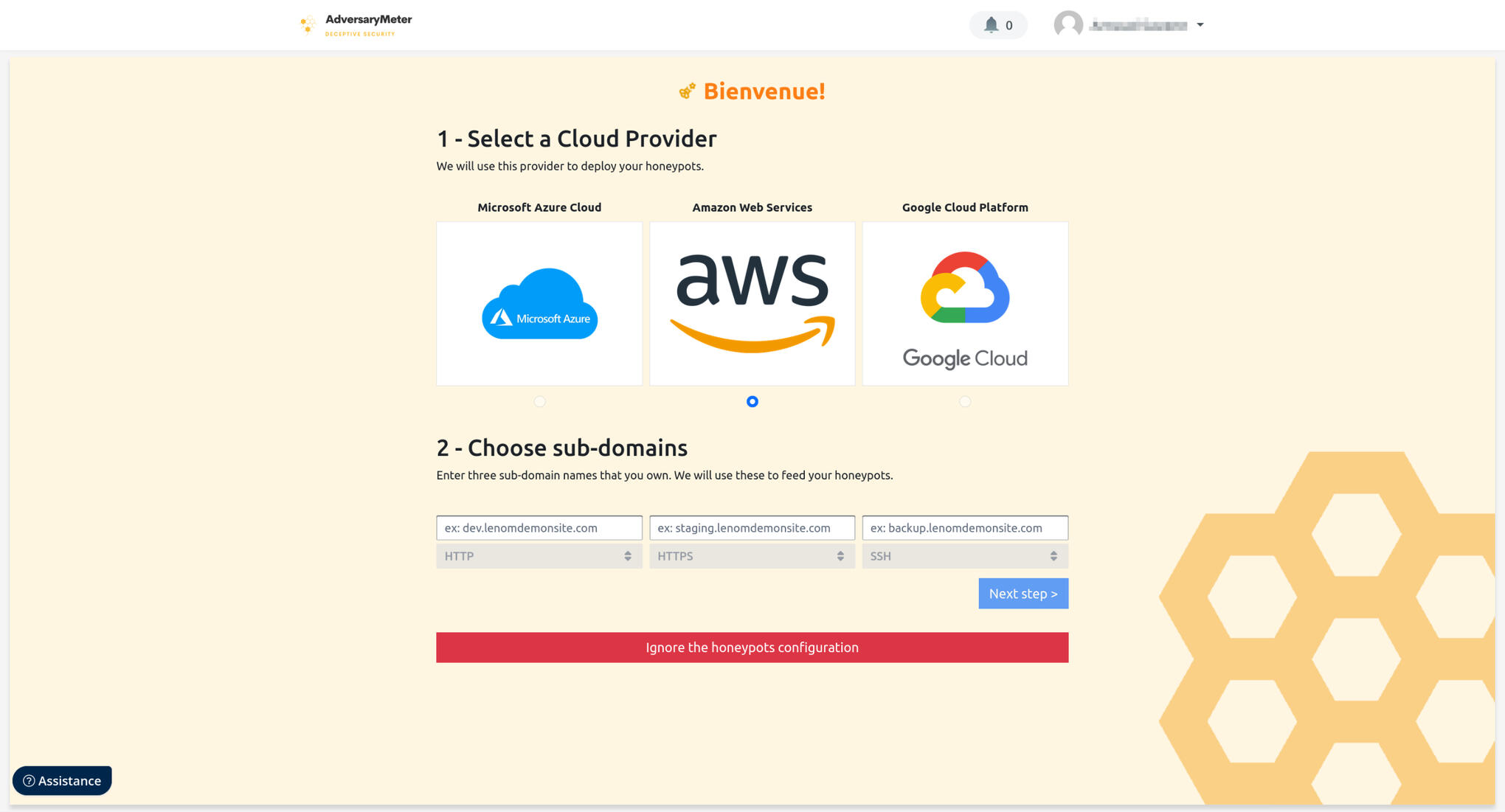
Honeyforge
The ultimate solution for constructing and deploying honeypots that stand guard on the internet's frontline. AdversaryMeter empowers you to strategically position honeypots to attract potential threats before they even reach your network. You're not just defending against cyberattacks; you're shaping the battlefield to your advantage.

Tailored Decoys
Cybermirage
By ingeniously incorporating the ability to replicate your existing resources, AdversaryMeter takes the foundation laid by your Web Application Firewall to the next level. Like a digital chameleon, it dynamically reconfigures your WAF to not only reroute suspect traffic away from your vital assets but also seamlessly deploys exact copies of your authentic resources as decoys.
VULNERABILITY SCANNER
Replay Attacks
AdversaryMeter's decoys mimic your resources, enticing attackers and slowing their progress. This interaction provides valuable insight into their methods. Our vulnerability scanner leverages this data to simulate these attacks (in addition to our 50,000 pre-recorded scenarios) on your real assets, empowering you to gauge your system's resilience firsthand.

Key Benefits
Why choose us?
Our approach: restore a balance between offense and defense by discreetly inserting decoys among your authentic resources, such as your websites or access points.What does it mean for you? A centralized place to manage the security of your exposed infrastructure and the quickest way to improve your security based on realworld metrics.
Startup
25€ / month
Best for startups or small companies with few internet-facing servers.
1 team
Unlimited users
Up to 3 honeypots
Up to 3 assets monitored
Business
75€ / month
Best for mid-sized companies with a handful of internet-facing servers and a few services providers.
1 team
Unlimited users
Up to 3 honeypots
Up to 10 assets monitored
Services providers delegation
Enterprise
Contact us
Best for enterprises with many internet-facing servers and a lot of services providers.
Unlimited teams
Unlimited users
Unlimited honeypots
Unlimited assets monitored
Services providers delegation
SOC integration
Subscribe to our Newsletter
Get monthly cybersecurity tips straight to your inbox.
ComputableFacts - 178 boulevard Haussmann 75008 Paris - 844389882
Thank you!
Thank you for signing up. You will be the first to know about new releases and special projects. Stay tuned.